Just In
- 9 hrs ago

- 11 hrs ago

- 11 hrs ago

- 12 hrs ago

Don't Miss
- Sports
 Who Won Yesterday's IPL Match 34? LSG vs CSK, IPL 2024 on April 19: KL Rahul Stellar Batting Show Decimate Chennai Bowling
Who Won Yesterday's IPL Match 34? LSG vs CSK, IPL 2024 on April 19: KL Rahul Stellar Batting Show Decimate Chennai Bowling - Finance
 Rs 17/Share Dividend: Record Date On April 26; Buy The ICICI Group Stock To Be Eligible?
Rs 17/Share Dividend: Record Date On April 26; Buy The ICICI Group Stock To Be Eligible? - Movies
 Chief Detective 1958 Episode 2 OTT Release Date, Time, Platform: When & Where To Watch? What To Expect? DEETS
Chief Detective 1958 Episode 2 OTT Release Date, Time, Platform: When & Where To Watch? What To Expect? DEETS - Lifestyle
 Golden Rules To Follow For Happy Marriage For A Long Lasting Relationship
Golden Rules To Follow For Happy Marriage For A Long Lasting Relationship - News
 Chinese President Xi Jinping Orders Biggest Military Reorganisation Since 2015
Chinese President Xi Jinping Orders Biggest Military Reorganisation Since 2015 - Education
 Exam Pressure Does Not Exist; Studying Punctually is Crucial; Says Aditi, the PSEB 2024 Topper
Exam Pressure Does Not Exist; Studying Punctually is Crucial; Says Aditi, the PSEB 2024 Topper - Automobiles
 Suzuki Swift Hatchback Scores 4 Star Safety Rating At JNCAP – ADAS, New Engine & More
Suzuki Swift Hatchback Scores 4 Star Safety Rating At JNCAP – ADAS, New Engine & More - Travel
 Journey From Delhi To Ooty: Top Transport Options And Attractions
Journey From Delhi To Ooty: Top Transport Options And Attractions
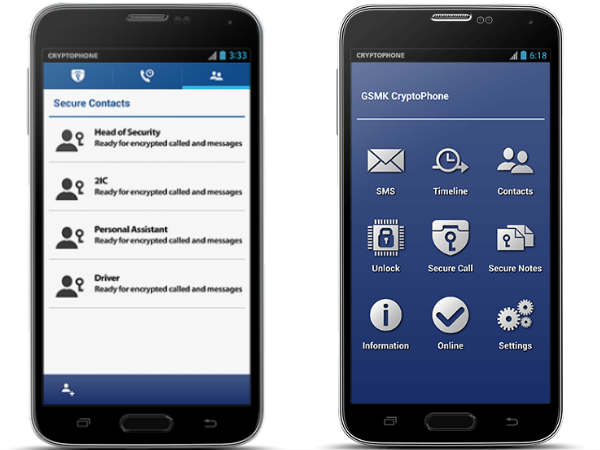
GSMK CyptoPhone Is The Most Secure Phone: What's the Need, Technologies Used and More
Can you believe that this phone can't be snooped on?
Until the launch of the Cryptophone, a phone that can scramble calls so that the conversations can't be listened to was like a novelty item seen in the James Bond movies.

With the extensive eavesdropping on people, especially the heads of state in the U.S. demanded a phone that can't be snooped on. That's when Goldsmith, a Las Vegas-based manufacturer came up with a device dubbed GSMK CryptoPhone that is priced pretty high at around $3,500. The company uses a version of the Android OS that is licensed from GSMK, a German company. This version of Android is tweaked to be secure by adding call encryption and fixes to the security flaws.
Also Read: HTC 11 might come with Snapdragon 835, nifty screen, high-end RAM and Storage
The sales of these devices were pretty good as almost 100,000 units of the handset were sold across the world in a few months. Notably, secure phones are not completely new. Back in the 1970s, the NSA came up with a secure telephone unit featuring an ordinary push button landline phone that is connected to a crate-sized scrambler for security purposes.
Also Read: Unannounced Moto Cedric Smartphone Spotted Running Android Nougat
Now, let's take you through some of the features and technologies used in the CryptoPhone from below.
Snooping and interception are the reasons
These days, smartphones can be infested by malware that is transmitted through calls, device location, data, etc. Telecommunication interception is an lawful interception that is used for governmental purposes. But, it doesn't restrict the use of this practice for other requirements. Even long time storage of the call content and traffic data is something that unlawful and this is happening in many countries since decades. So, encryption is the only way to protect privacy and its a prudent choice as well.

Audio compression
CryptoPhone uses audio compression that makes use of highly optimized voice codecs supporting several network technologies. This will ensure that the call that is placed gets through even when the throughput of the network is limited.
Click Here for New Smartphones Best Online Deals

Transport technology
The CryptoPhone units give the complete flexibility for the users to choose between the classical circuit switched data connections or the current generation Internet Protocol based communication links. The ability to choose one of the these transport technologies will offer the users a complete range of communication networks starting from analog telephone lines to the 3G/UMTS high-bandwidth connections.

Encryption engine
All the CryptoPhone models use a single encryption engine that is a portable multi-platform cryptographic module offering authentication, encryption, key exchange, secure memory abstraction, and message integrity verification. These handsets use strong encryption algorithms and lengthy keys that let the products provide enough security and peace of mind to the users.
Also Read: Your Samsung Galaxy Note 7 Might Stop Working Any Time Soon
Software architecture
The CryptoPhone's architecture was designed in such a way that it offers 360-degree protection not only against the messages and calls that are confidential, but also attacks against the device. The CryptoPhone features a hardened OS, voice and message encryption, and secure storage.

Cryptographic key is needed
Remember that secure calls work only when calls are placed from one CryptoPhone to the CryptoPhone. In order to setup a highly secure connection, both the handsets will create a cryptographic key is based on random background noise. All these activities take place on the CryptoPhone itself ensuring that no unprotected data will leave the device.
Also Read: 6 Easy to Use and Free Apps That'll Make Your Teamwork More Effective

Price is expensive, but its not for usual consumers
CryptoPhone is priced at $3,500 that is pretty expensive, but this includes three years of service and not the call charges. Moreover, this device is not meant for the individuals and small business users. Also, the consumers have not joined the security rush for now. Maybe in the future, the masses might look for secure communication products that will keep them away from being tracked online. For now, the apps that help them send self-destructing messages or the anonymous bulletin boards are keeping them satisfied.
-
99,999
-
1,29,999
-
69,999
-
41,999
-
64,999
-
99,999
-
29,999
-
63,999
-
39,999
-
1,56,900
-
79,900
-
1,39,900
-
1,29,900
-
65,900
-
1,56,900
-
1,30,990
-
76,990
-
16,499
-
30,700
-
12,999
-
62,425
-
1,15,909
-
93,635
-
75,804
-
9,999
-
11,999
-
3,999
-
2,500
-
3,599
-
8,893












































