How Truecaller Works And Here Is All You Need To Know! [Pros And Cons]
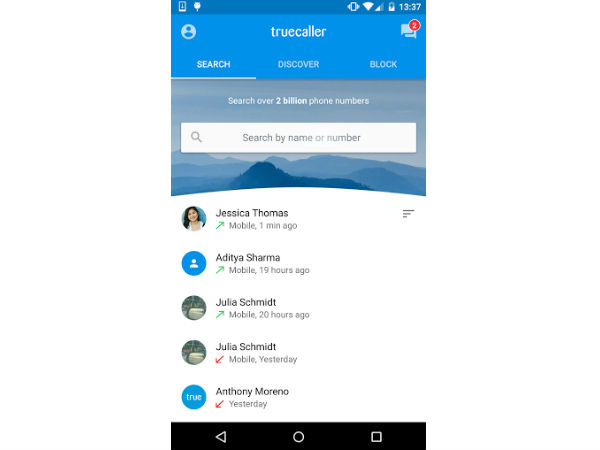
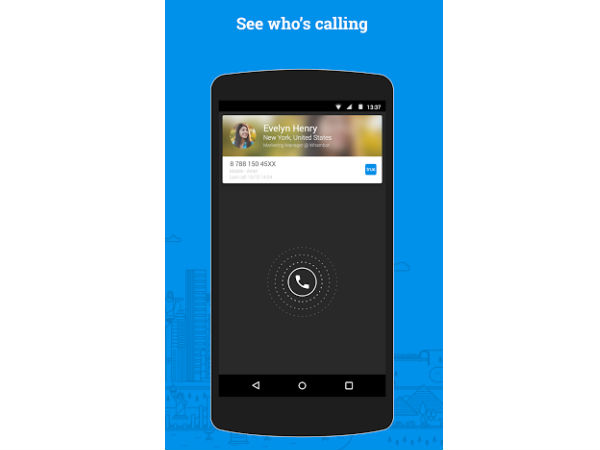
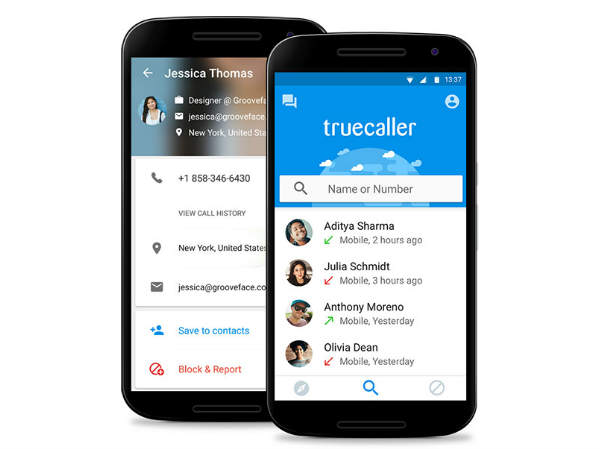
Truecaller, an app that goes beyond the limitations of today's phonebook apps. The Truecaller app helps people always have access to the right information, people and businesses they need. As we all know the app lets users to search for contact information, identify incoming calls, and also block calls that you don't want to receive.
![How Truecaller Works And Here Is All You Need To Know! [Pros And Cons] How Truecaller Works And Here Is All You Need To Know! [Pros And Cons]](https://images.gizbot.com/img/2016/03/08-10-1457586576.jpg)
Many smartphone users are using Truecaller to trace out a lot of spam calls they get everyday. So, did you ever wonder how Truecaller actually works? Well, it acts on a give and take scenario, if you want those unknown numbers then you have to be a part with your phonebook contacts.
SEE ALSO: Here Are 10 New WhatsApp Features That Rolled Out In 2016
Apparently everyone who has installed the app has surrendered his phonebook. The data is crowd-sourced from the million of users who have installed the Truecaller app on their device. So out of all the people who know you and have your contact number stored against your name in their phone, if even one person uses the Truecaller app, your contact details would end up in the Turecaller database.
Well, this post will give you an insight on the pros and cons of Truecaller app, have a look at the slider below to know more.
Pros
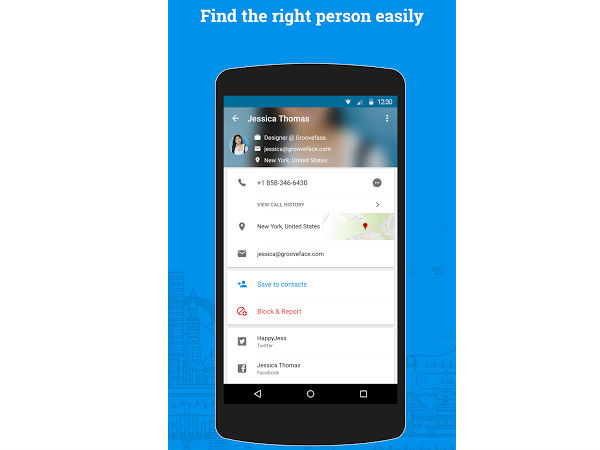
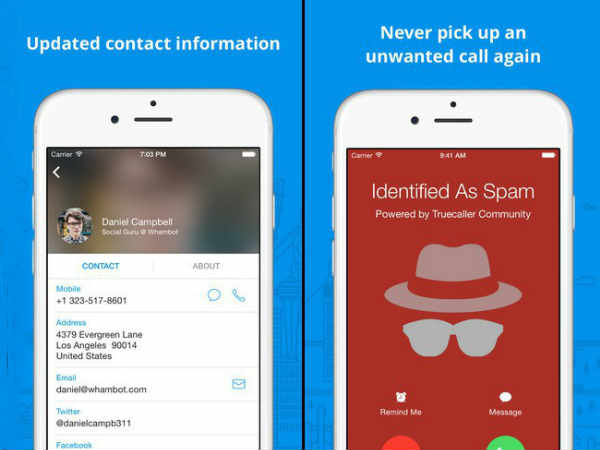
Truecaller allows you to find mobile phone location of the number in search.
Pros
The app also comes with a 'Who viewed my profile' functionality, so that you can keep a track on who is viewing your number.
Pros
You can find caller from phone number. Similar to reverse phone lookup
Pros
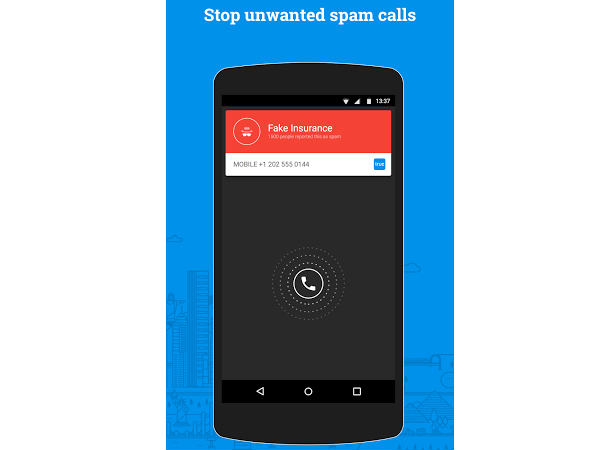
It allows you to block such spam numbers and report them to Truecaller database to mark it as spam so that others may also not suffer from this number

Cons
Caller ID does not work in all areas

Cons
Truecaller requires Internet connection for it to work
Cons
No guarantee of information security
Cons
It infringes on privacy issues.



 Click it and Unblock the Notifications
Click it and Unblock the Notifications






























-1763362932432.svg)