Anonymous Declares War on ISIS After Paris Attack: Here's How They Did It!
In reply to the ghastly attack in Paris, the International hacking collective "Anonymous" has declared cyber war on the self acclaimed ISIS terror group, that left 129 people killed and 350 injured. Aftermath the terror attack, the French member from Anonymous warns ISIS saying " expect numerous cyber attacks."

As promised, the Anonymous group has started leaking the personal information of suspected extremist. Moreover, they have assembled the list of Twitter accounts and successfully removed more than 5,500 accounts of the extremist.
SEE ALSO: Micromax Canvas Amaze: 10 Best And Worst Features Of The Smartphone
Anyhow, none of the informations shared could be confirmed, because the activist have wrongly identified alleged extremist in the past. But what is this attack all about? What damage it can cause, if one wants to attack the organization?
To clear the air, GizBot has come up with five tactics that has been used by the group in past activities. Do swirl through:

Hacking #1
By hacking into their accounts, the activists can access the private networks of terrorist organization and disseminate battle plans, operation names and other key informations, that can be helpful.

Hacking #2
Doxxing - The method of releasing the personal and private information of an individual person who got involved in the terrorist activities.
More often, the details obtained via "Doxxing" will be shared via anonymous and other publicly accessible channels like the website Pastebin, or internet forums like 4chan

Hacking #3
A DDoS or disturbed denial-of-service attack is an attempt to make online service unaccessible by crushing the website with far more traffic from multiple sources to the targetted computer system. When the system gets over run it shuts down automatically making it dysfunctional.
Anonymous has already tried this attack in multiple instances like The Church of Scientology to the municipal computer system of Ferguson.
Hacking #4
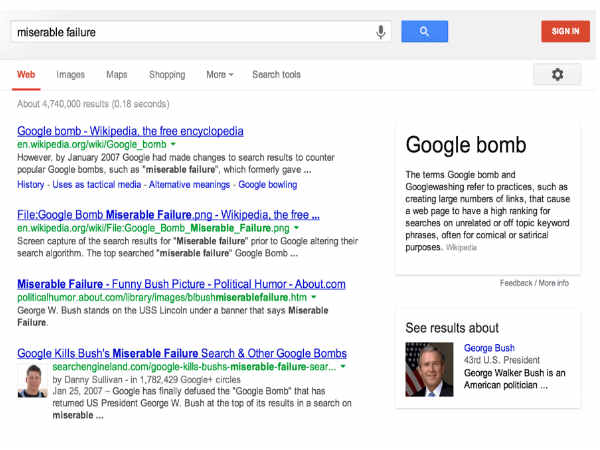
Google Bomb - Its an act of linking en masse to an alternative definition, to impact the Google results that come up when someone searches that word.
To make it clear, let me give you a Example: In 2003, the Google bomb of the phrase "miserable failure" has been linked to the biography of George W Bush as most relevant link, after the repeated usage of the phrase as the text to link to GW Bush's biography.

Hacking #5
This is the basic thing that every hackers can do. There are varities of hacking including Remote code execution attack, cross site request forgery attack, social engineering attack and more. Since, the ISIS is active on social media to recruit new members, this will be the like course of action by the activists.



 Click it and Unblock the Notifications
Click it and Unblock the Notifications






























-1763362932432.svg)