This is how Apple reacted to FBI in the iPhone case!
On December 2, 2015, 14 people were killed and 22 seriously injured when two perpetrators, including Syed Farook, carried out a planned terrorist attack on the peaceful county of San Bernardino in Califronia, US.
The perpetrators, Syed Rizwan Farook and Tashfeen Malik, a married couple living in the city of Redlands, targeted a San Bernardino County Department of Public Health training event and holiday party, of about 80 employees, in a rented banquet room.
SEE ALSO: 10 Secret Facts About the life of Google CEO Sundar Pichai!
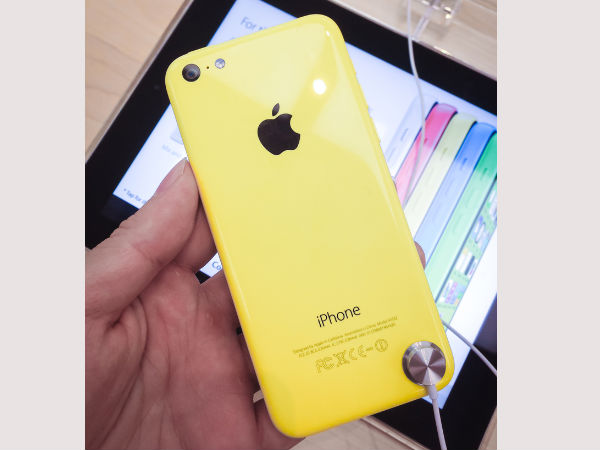
This attack followed serious investigation from the FBI and among the evidence was an iPhone 5C, owned by the same Syed Farook. On February 9th 2016, the FBI announced that it had been unable to access the data on that iPhone, due to Apple's secure encryption in the software. Here is a step-by-step guide as to how the Apple vs FBI debacle took place and what will be its future implications.

#1
As mentioned above, the terrorist attack took place in December last year and was a planned one, on the county of San Bernardino in California. The attack was followed by a wild car chase and shootout between the police and the attackers. This confirmed the fact that the terrorists were part of a big strategy plan and complete evidence had to be extracted in order to avoid any such future incidents.
#2
After the attack, the FBI immediately got onto the case and the search for all necessary evidence begun. Upon the completion of the search, the FBI came across an iPhone 5C - owned by Farook - that probably had some conclusive evidence that they didn't quite find in the other products and equipment that was part of the case. Apparently, this iPhone contained some secret codes or messages that the perpetrators used to communicate with the mastermind.

#3
This iPhone had a fingerprint as well as a passcod lock on it, preventing the FBI from accessing data inside it. Earlier, the FBI has used different techniques like punching, which involves a system that enters all possible key combinations to eventually unlock the device. This was, however, a problem in this case as the iPhone was programmed to wipe out or reset all the data if a specific number of incorrect entries were submitted on the device. The FBI now made this information public and requested Apple, maker of the iPhone, to help them create a special software that acts as a backdoor for the FBI to easily access all their Apple devices that contained sensitive and crucial data.

#4
Apple is the world's most valuable corporation and its reaction is what makes it the best. Just days after FBI's request - command, rather - to create another backdoor software, Tim Cook, CEO-Apple, posted a long message on the official site explaining his rejection for this order. He wrote,
"The FBI may use different words to describe this tool, but make no mistake: Building a version of iOS that bypasses security in this way would undeniably create a backdoor. And while the government may argue that its use would be limited to this case, there is no way to guarantee such control."
He explained this stance by saying,
"The government suggests this tool could only be used once, on one phone. But that's simply not true. Once created, the technique could be used over and over again, on any number of devices. In the physical world, it would be the equivalent of a master key, capable of opening hundreds of millions of locks - from restaurants and banks to stores and homes."

#5
Immediately after Apple's official statement came from Tim Cook, the FBI filed a case in California courts, blaming Apple for interference and non-cooperation with national security matters. This ruling was expected to define the path of privacy rules in the US.
Then last week, all of a sudden, on the eve of a court hearing in the case, the FBI asked for the proceedings to be halted, saying it had devised a new technique that might allow it to gain access. A week later, the FBI told the court that it had recovered the data on Farook's iPhone and no longer needed Apple's help, thereby withdrawing the case.

#6
The FBI had argued that only Apple was the one who could help it unlock Farook's iPhone. This part was crucial because the law the FBI invoked, called the All Writs Act, requires the FBI to make reasonable efforts before forcing a corporation like Apple to help in its investigation. For weeks, the FBI had claimed that it had exhausted all other methods and was turning to Apple as a last resort.
Apple's win in this case is sure to increase the stature of Apple CEO Tim Cook. The San Bernardino terrorism case was in many ways a kill or get killed kind of deal for Apple, forcing the company to effectively defend the privacy rights of one of the most controversial mass murderers in recent times. By standing up to the FBI in this case, and emerging unscathed, Apple will be stronger in future situations.



 Click it and Unblock the Notifications
Click it and Unblock the Notifications





























-1763362932432.svg)