Facebook 16000 Users Credentials Slipped by PokerAgent Botnet
An analysis by a security firm ESET, noted that over 16,000 account credentials of Facebook was stolen by Poker Agent. The threat was primarily active in Israel, which was identified a year back. It was designed basically to steal the information regarding payment from the users of Facebook who played Zynga poker, the most played online poker game.
It was found that in March 2012 there were at least 800 computers that were affected and the database of the attacker contained over 16,000 credentials of Facebook accounts. The malware, from the moment it is on the device, logs on to the Facebook accounts using the credentials that were stolen. The malware then finds the stats of Zygna Poker and the payment information that is saved in the respective Facebook accounts of the users.
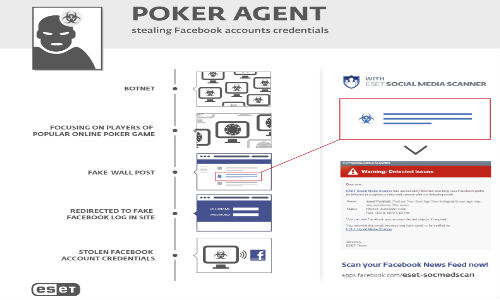
It is seen that the malware is coded in C# and this makes it easy to decompile. The Trojan is downloaded into a device using a downloader component that was available on the web. The victims appear to have been fooled into downloading the Trojan.
ESET had been tracking and monitoring Botnet since 2012 March. The malware for now does not seem to be spreading actively. The experts are unable to determine how it spread and its source but suspect a possibility of the same via Facebook. Cyber world criminals had stopped spreading the malware in February 2012 but the law enforcement and CERT officials of Israel have been notified. An investigation has now been launched. The social networking site, Facebook, in the mean time has implemented needed measures to curb such risks.



 Click it and Unblock the Notifications
Click it and Unblock the Notifications





























-1763362932432.svg)