10 Pro-Tips To Protect Your Smartphone From Malicious Threats
Your smartphone houses a lot off information including includes things from personal email, social media accounts to bank accounts.
There have been many incidents regarding the data loss of smartphones via malware or hackers who try to hack into smartphones to retrieve data and destroy it. Other incidents state that data has been corrupted or the phone itself is behaving weirdly.
SEE ALSO: 8 Simple Steps To Fix Water Damaged Smartphones
Well all these problems can be solved if smartphone users follow certain tips and tricks to protect their devices along with their data. Smartphones are famous for their flexibility as you can customize anything you want but their remains potential risk at everything. You need to take every measure possible to ensure its security, read on to know more.

Smartphone Security
One of the easiest ways to protect smartphone information is to lock your device, by either using a pin code or pattern. These days new smartphones are coming with biometirc sensor, which allows you to lock smartphone with your fingerprint.

Smartphone Security
Apps requires some access to the data you have store on your smartphone, which means some apps could maliciously acquire access to your data. So before you download any app, make sure it is from a trustworthy app developer and read the app review or research the app to determine if it is trustworthy.

Smartphone Security
Smartphone maker frequently rolls out security update for the device. In order to take advantage of this, you can set your phone to automatically update to get security updates. It will help your smartphone to protect from new security threats that are intended to steal your information.

Smartphone Security
When your are not using services like GPS, Bluetooth and Wi-Fi on your smartphone, it is recommended to turn off them. It not only constantly drain the battery, but also constantly trying to locate wireless networks, other Bluetooth devices and sharing your locations, which can also be a routes for malicious content.

Smartphone Security
BlackBerry smartphones are known for encryption and security, as every single operation in the smartphone is encrypted. Android also allows you to encrypt all the data on your smartphone. Users need to set key either password or PIN each time the device is turned on to decrypt all the data.

Smartphone Security
According to security experts, devices in workplaces are vulnerable to threats and other malware. If you are planning to use your personal device at work then please discuss about the issues with IT before configuring access and store work related data.
Smartphone Security
Even if you have lost your device, the Android Device Manager feature will allow you to track your (connected) device on Google Maps. It also enables the device to ring at full volume for five minutes and erase all the data instantly. To verify if it's enabled, you can go to the Settings >> Security >> Device Administrators. Here is a full guide on how to locate and delete data on your lost phone.

Smartphone Security
Additional protection for apps like Gallery and Messaging to protect private data is available on the play store. Apps like Gallery Lock and SMS lock can safeguard your data from being mishandled. Number of apps are available on Play Store that offer an additional level of protection for individual apps. Such apps ask you to set up a password or PIN code that needs to be entered whenever you open the particular protected apps.

Smartphone Security
Rooting Android device will give the ability to access the core of the phone and giving the user full permission and rights to install custom ROMS and even incompatible apps but, voids of the warranty. However, apps with root access gets unhindered access to your device file system which may cause more damage and attract malware to your device.
Smartphone Security
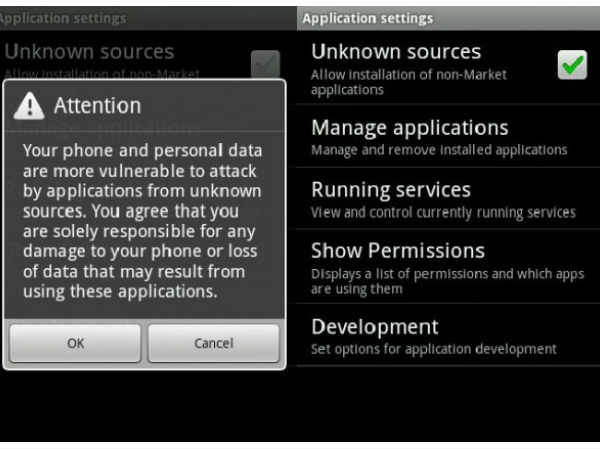
Apps on the Google Play Store are not curated as diligently as the ones available on Apple's App Store but, it is still the safest place to download and install apps on Android platform. Installation files (APKs) sourced from third-party sites should be dealt with caution as they might hide malware or spyware. Users need to uncheck the unknown source box if it has been selected.



 Click it and Unblock the Notifications
Click it and Unblock the Notifications






























-1763362932432.svg)