Windows 7 Meltdown patch makes users prone to vulnerability
Microsoft Windows latest vulnerability allows processes to access all data in the memory and also allow them to read or write anywhere in the Kernel memory.
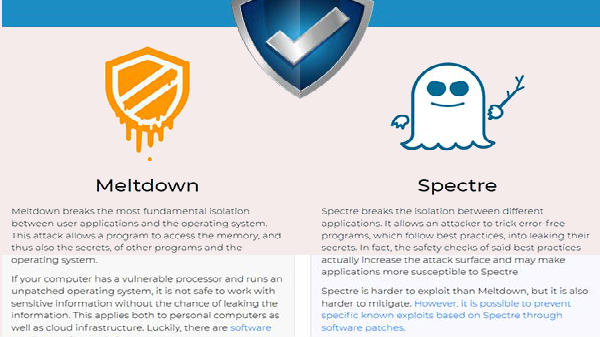
Almost all the devices were affected by the Meltdown and Spectre security flaws. However, all the companies rolled out various updates and patches for the security of their user base. Microsoft was also not left behind, with its user base being attacked by the Meltdown and Spectre flaws the company was quick enough to roll out patches for the same. Microsoft took the situation quite seriously like the other tech giants tried to provide quick resolution of the situation to its users. The patch for Windows 7, Windows 8.1, and Windows 10 devices was out following the security flaws, however as per some reports from the web the new patch which Microsoft is rolling out for the Meltdown security flaw is leaving the users vulnerable to data theft.

As per some reports from The Beebom, the patch which was rolled out for Meltdown on Windows 7 (64-bit) and Windows Server 2008 R2 doesn't improve the situation rather it marks a big question mark on the security of the users. The latest vulnerability allows processes to access all data in the memory and also allow them to read or write anywhere in the Kernel memory.

The flaw was first noticed by Ulf Frisk who is a security researcher. According to Frisk, "Windows 7 already did the hard work of mapping in the required memory into every running process. Exploitation was just a matter of reading and write to already mapped in-process virtual memory," "Once read/write access has been gained to the page tables it will be trivially easy to gain access to the complete physical memory unless it is additionally protected by Extended Page Tables (EPTs) used for Virtualization. All one [has] to do is to write [one's] own Page Table Entries (PTEs) into the page tables to access arbitrary physical memory" he further adds.
Frisk has also advised all the admins and the users of Windows 7 and Windows 2008R2 to install Microsoft's March patch to resolve it. Windows 10 and Windows 8.1 are however unaffected which brings a breath of relief for the users.



 Click it and Unblock the Notifications
Click it and Unblock the Notifications






























-1763362932432.svg)