Kaspersky Discovers The Most Sophisticated Android Trojan
IT security firm Kaspersky has reported that it has recently discovered an Android Trojan, which they are calling as the most sophisticated malware yet. Upon analysis of an android application, Kaspersky discovered a file (DEX), which turned out to be a multi-functional Trojan. Dubbed as Backdoor.AndroidOS.Obad.a or "Obad", the malicious program can send SMS to premium-rate numbers, download other malware programs, install them on the infected device and also transfer them via Bluetooth. It is also said to be capable of performing remote commands in the console.
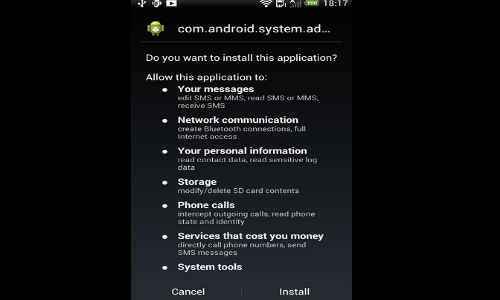
The trojan apparently takes advantage of an error in the DEX2JAR software - a program typically used by analysts to convert APK files into the more convenient Java Archive (JAR) format. Obad utilizes multiple strings of encryption and highly complicated coding to remain concealed.
Also, the malware exploits an error in the AndroidManifest.xml file, which is present in every Android application, to gain access to a device. Once inside, it is said to raise havoc, as it gains access to Device Administrator privileges. What's worse is Obad does not have an interface and works in background mode. Meaning, once inside, it will remains invisible, making it impossible for the users to delete it.
Kaspersky has already informed Google about the Device Administrator vulnerability in Android. The IT security firm writes in it's blog that despite having such impressive capabilities, the malware isn't wide spread. "Over a 3-day observation period using Kaspersky Security Network data, Obad.a installation attempts made up no more than 0.15% of all attempts to infect mobile devices with various malware" read the blog.



 Click it and Unblock the Notifications
Click it and Unblock the Notifications





























-1763362932432.svg)