7 common email security protocols explained
Information on the internet can be handled dangerously. Most of your online footprint stems from the emails you send and receive. So, it seems obvious to us that our emails should have some security measures set up, but most of them don't. Some are simple enough to be broken and hacked into. Given below is a list of some commonly used security protocols and how they work.

SSL/TLS
SSL and TLS are application layer protocols (rules) most commonly used. Transport Layer Security (TLS) is the successor and it provides a base-level encryption. Usually, an email client, such as Gmail, while sending and receiving mails connects to an email server via TCP. The TLS adds privacy and security while establishing a connection between client and server.

Digital Certificates
Digital Certificates encrypt your mail details using cryptography. These belong to a class called Public Key Encryption. Your Digital Certificate acts as a public key using which they can lock the emails they're sending you. You can decrypt the emails using a private key that you'll posses. This is how Bitcoins work.

Sender Policy Framework
Sender Policy Framework (SPF) is a protocol that authenticates domains and prevent them from being spoofed. A domain can be used to mask the intents of hackers and cyber criminals. SPF helps a server identify if the message was sent through a legitimate domain or not.
DKIM
DKIM is an extended version of SPF. DomainKeys Identified Mail looks after the safety of your email while it's in transit. It works in two ways. First, it uses digital signatures to check if a domain sent the mail. Then, it traces the domain to see if it actually authorized sending the mail. It's a double-layered protocol.
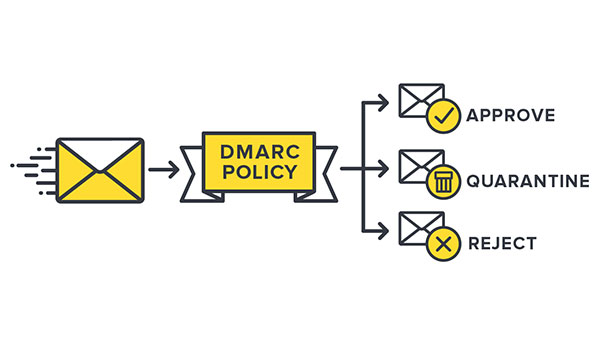
DMARC
DMARC stands for Domain-Based Message Authentication, Reporting and Conformance. It is an authentication protocol that checks the validity of SPF and DKIM and instructs the provider on handling incoming messages. However, DMARC hasn't seen good rates of adoption. And it isn't foolproof either.

S/MIME
These are end-to-end encryption protocols. S/MIME is designed to encrypt email contents, but leaves the details, such as recipient, sender, open. These have been used for a long time and chances are that your email client uses them too. They require a digital signature such that only the recipient is capable of decrypting your email.

PGP
PGP and OpenPGP are end-to-end encryption protocols, with the latter being open-source. Open Pretty Good Privacy (PGP) works just as S/MIME, meaning just the contents are encrypted and a third-party can gather recipient and sender details, which constitute the metadata. OpenPGP gets timely updates and is free to use. Gpg4Win for Windows and GPGSuite for Mac should be a place to start.



 Click it and Unblock the Notifications
Click it and Unblock the Notifications





























-1763362932432.svg)